Table of Contents
ToggleIntroduction
Ethical hacking is an important aspect of cybersecurity. It involves identifying vulnerabilities and weaknesses in computer systems and networks in order to protect them from malicious attacks. Governments and businesses are realizing the importance of cybersecurity and are taking steps to protect their assets. So, in recent years, the demand for ethical hackers has increased significantly. In 2023, the demand for ethical hackers will continue to increase as more organizations adopt digital technologies and the threat landscape evolves. The implementation of new technologies such as the Internet of Things (IoT), blockchain, and artificial intelligence (AI) will also present new challenges and opportunities for ethical hackers. As a result, there will likely be a continued need for skilled ethical hackers.
Don't miss out on your chance to work with the best
apply for top global job opportunities today!
What is Ethical Hacking?
Ethical hacking, also known as penetration testing or white-hat hacking, refers to the practice of deliberately and legally exploiting computer systems, networks, or applications with the authorization of the system owner. Ethical hackers, also known as security researchers or white-hat hackers, use their technical skills and knowledge to identify vulnerabilities, weaknesses, and security flaws in digital systems.
What is the primary objective of Ethical Hacking?
The primary objective of ethical hacking is to assess the security positioning of an organization’s digital infrastructure and provide recommendations for enhancing its security. By simulating real-world cyber-attacks, ethical hackers help organizations identify potential entry points and vulnerabilities that malicious hackers could exploit. This proactive approach enables organizations to strengthen their defences, protect sensitive information, and mitigate the risk of data breaches, financial losses, or reputational damage.
What do Ethical Hackers do?
The responsibilities of ethical hackers vary based on the requirements of their employers. Their activities typically include penetration testing, vulnerability assessments, and implementing various strategies to ensure the security of their organizations. Some of their tasks encompass:
- Preventing unauthorized access and theft of sensitive data.
- Identifying vulnerabilities in networks and systems.
- Assisting in fortifying weak points by implementing robust defences.
- Establishing secure networks to deter security breaches.
- Safeguarding information and assets to build trust with customers and investors.
How do Ethical Hackers assess the security of systems?
Ethical hackers employ a variety of techniques and methodologies to assess the security of systems. Here are some common approaches used by ethical hackers during security assessments:
- Reconnaissance: Ethical hackers gather information about the target system or organization using publicly available resources, such as search engines, social media, and company websites. This helps them understand the system’s architecture, potential vulnerabilities, and attack surface.
- Vulnerability Scanning: Ethical hackers use specialized tools to scan networks, systems, and applications for known vulnerabilities. These tools automatically identify weaknesses, misconfigurations, or outdated software versions that could be exploited by attackers.
- Penetration Testing: This is the core activity of ethical hacking. It involves attempting to exploit identified vulnerabilities in a controlled manner, mimicking the actions of a real attacker. Ethical hackers simulate various attack scenarios, such as network attacks, web application attacks, or social engineering techniques, to determine the effectiveness of existing security controls.
- Social Engineering: Ethical hackers may employ social engineering techniques to test the human element of security. They attempt to manipulate employees into revealing sensitive information or performing actions that compromise security. This can include phishing emails, phone calls, or physical onsite attempts to gain unauthorized access.
- Wireless Network Testing: Ethical hackers assess the security of wireless networks by attempting to bypass authentication, intercept network traffic, or exploit misconfigurations in Wi-Fi networks. This helps identify potential weaknesses in wireless security and ensures proper protection of sensitive data.
- Web Application Testing: Ethical hackers scrutinize web applications to identify vulnerabilities such as input validation flaws, SQL injection, cross-site scripting (XSS), or insecure session management. They employ manual and automated techniques to evaluate the resilience of web applications against potential attacks.
- Exploit Development: Ethical hackers may develop or use existing exploits to demonstrate the impact of identified vulnerabilities. This involves crafting malicious code or leveraging publicly available exploit frameworks to gain unauthorized access or control over the system.
- Post-Exploitation Analysis: After successfully compromising a system, ethical hackers analyze the extent of the impact and potential further exploitation. They explore the consequences of a successful attack and provide recommendations to mitigate similar risks in the future.
Recommended: How to Start a Career In Cybersecurity In 2023?
What are the types of Ethical Hacking?
There are different types of ethical hacking methods, depending on the level of knowledge and access that the ethical hacker has about the target system. Some of them are as follows:
- Black-box Testing: In black-box testing, the ethical hacker doesn’t have any prior knowledge of the system and is testing it from an outsider’s perspective. This type of testing simulates a real-world attack scenario and helps to identify unknown vulnerabilities and weaknesses. However, it can also be time-consuming and inefficient, as the ethical hacker has to try various methods to find a way in.
- White-box Testing: In white-box testing, the ethical hacker knows everything about the system, how it works, and its architecture. This type of testing allows the ethical hacker to perform a thorough and comprehensive analysis of the system and its security measures. However, it can also be unrealistic and impractical, as the ethical hacker has access to information that a real attacker may not have.
- Gray-box Testing: In gray-box testing, the ethical hacker has some knowledge of the system, but not all. This type of testing combines the advantages of both black-box and white-box testing, as it allows the ethical hacker to perform a realistic and efficient assessment of the system. However, it can also be challenging and complex, as the ethical hacker has to balance between what they know and what they don’t know about the system.
- Web Application Testing: In web application testing, the ethical hacker focuses on testing web applications and websites for security vulnerabilities. This type of testing involves using various tools and techniques to exploit common web application attacks such as SQL injection, cross-site scripting, denial-of-service, etc. Web application testing is crucial for ensuring the security and functionality of web applications that handle sensitive data and transactions.
- Network Testing: In network testing, the ethical hacker focuses on testing network infrastructure and devices for security vulnerabilities. This type of testing involves using various tools and techniques to scan, monitor, and analyze network traffic and activity for any signs of intrusion or anomaly. Network testing is essential for ensuring the security and performance of network systems that connect various devices and applications.
- System Testing: In system testing, the ethical hacker focuses on testing computer systems and operating systems for security vulnerabilities. This type of testing involves using various tools and techniques to access, manipulate, and control system resources and processes. System testing is important for ensuring the security and stability of computer systems that run various applications and services.
To be an ethical hacker, you need to have a combination of technical and soft skills that can help you identify and resolve security vulnerabilities in computer systems and networks. Some of the skills required to be an ethical hacker are:
- Networking skills: You should understand how computer networks work, data is transmitted and received, network protocols operate, and how to configure and troubleshoot network devices. You also need to know how to perform network reconnaissance, scanning, enumeration, and sniffing.
- Penetration testing skills: You should know how to conduct penetration testing. Penetrating testing is a method of evaluating the security of a system or network by simulating an attack from a malicious source. You need to know how to use various tools and techniques to exploit vulnerabilities, gain access, escalate privileges, maintain persistence, and cover your tracks.
- Programming skills: You should know how to write code in different languages, such as Python, C/C++, Java, Ruby, Perl, etc. You also should know how to reverse engineer existing code, debug and analyze programs, and create scripts and exploits.
- Linux skills: You should know how to use the Linux operating system. You also should have an understanding on how to navigate the Linux file system, use command-line tools, configure, and administer Linux servers, and customize Linux distributions.
- Cryptography skills: You should know how to use cryptography. Cryptography is the science of securing data using mathematical techniques. You should also have knowledge of how to encrypt and decrypt data, generate and crack passwords, use digital signatures and certificates, and understand different types of encryption algorithms.
Apart from these technical skills, you also need some soft skills that can help you communicate effectively with your clients and colleagues, such as:
- Problem-solving skills: You should be able to think creatively and analytically to find solutions for complex security challenges. Also, you should research and learn new technologies and methods, and adapt to changing scenarios.
- Ethical skills: You should be able to follow the ethical principles and guidelines of ethical hacking, such as obtaining permission, respecting privacy, reporting findings, and avoiding damage. You should also understand how to distinguish between legal and illegal hacking activities and avoid any malicious or criminal intent.
- Communication skills: You should be able to communicate clearly and professionally with your clients and colleagues. You should also be able to explain technical concepts in simple terms, write detailed reports and documentation, and present your findings and recommendations.
What education is required to become an ethical hacker?
There is no standard education requirement to be an ethical hacker, but having a degree or certification in a relevant field can help you gain the necessary skills and knowledge. Some of the possible education options are:
A bachelor’s or master’s degree in computer science, information security, or mathematics: These degrees can help you learn the fundamentals of computer systems, networks, programming, cryptography, and other topics that are essential for ethical hacking.
A certification course such as Certified Ethical Hacker (CEH), GIAC Penetration Tester (GPEN), Offensive Security Certified Professional (OSCP), or Certified Penetration Testing Engineer (CPTE). These certifications can help you validate your skills and knowledge in ethical hacking and penetration testing and demonstrate your competence to potential employers.
A self-taught approach using online courses, books, blogs, podcasts, and other resources. If you have a passion for learning and a curiosity for hacking, you can also teach yourself the skills and techniques of ethical hacking using various online platforms and resources. However, this approach may require more time and effort, and may not be recognized by some employers.
Job Roles in Ethical Hacking
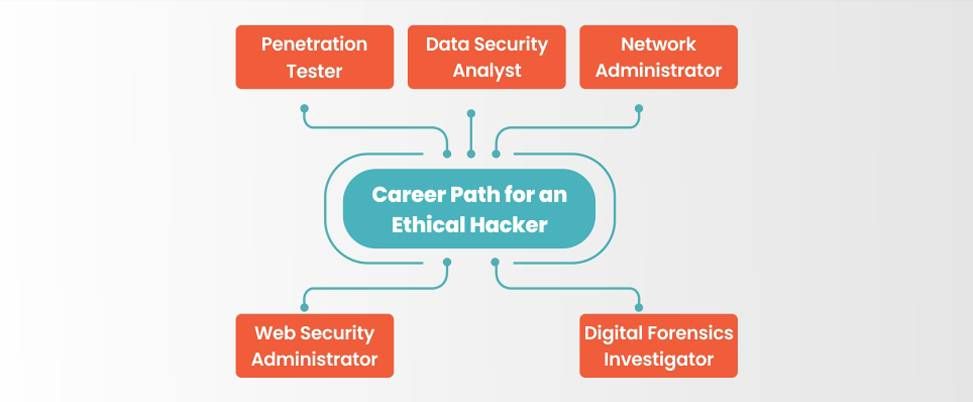
There is a wide range of ethical hacking jobs available in 2023, ranging from entry-level positions to more advanced roles. Here are a few examples of the types of positions you might encounter:
- Ethical Hacker/Penetration Tester: They are responsible for identifying and exploiting vulnerabilities in computer systems and networks to improve their security. They use various tools and techniques to simulate real-world attacks and test the effectiveness of security measures. They also prepare reports and recommendations on how to fix the vulnerabilities and prevent future attacks.
- Information Security Analyst: They assess security risks and vulnerabilities in computer networks and systems and develop strategies to prevent security breaches. They monitor and analyze security incidents and respond to them accordingly. They also implement security policies, standards, and best practices to ensure compliance with laws and regulations.
- Web Security Administrator: They are responsible for ensuring the security of web applications and websites. They perform web application penetration testing, code review, vulnerability scanning, and web server configuration. They also protect web applications from common attacks such as SQL injection, cross-site scripting, and denial of service.
- Network Security System Administrator/Manager: They are responsible for ensuring the security of network infrastructure and devices. They install, configure, maintain, and troubleshoot network security systems such as firewalls, routers, switches, VPNs, IDS/IPS, etc. They also monitor network traffic and activity for any signs of intrusion or anomaly.
- Security Consultant: They provide security consulting services to clients on various aspects of cybersecurity. They conduct security audits, assessments, tests, and reviews to identify security gaps and risks. They also provide security solutions, recommendations, training, and guidance to clients on how to improve their security posture.
- Application Security Executive: They are responsible for ensuring the security of software applications and products. They perform application security testing, code analysis, vulnerability assessment, and remediation. They also ensure that the applications comply with security standards and best practices.
Learn Linux
When it comes to hacking, professional hackers often opt for Linux operating systems due to their versatility and the fact that many other operating systems are built upon the Linux kernel.
UNIX/Linux-based operating systems are widely utilized to enhance the security of computer systems. These operating systems are free and open-source software, initially developed by AT&T in Bell Labs, and have made significant contributions to the field of security.
Therefore, it is essential to learn UNIX/Linux in order to acquire expertise in Ethical Hacking. Linux kernel-based operating systems are readily accessible, as they can be downloaded and used by anyone.
Here are a few examples of Linux kernel-based operating systems commonly used:
- Kali Linux
- Parrot Security OS
- BackBox
- BlackArch Linux
- Fedora Security Spin
- Caine
By learning these operating systems, aspiring ethical hackers can perform ethical hacking tasks effectively.
Ethical Hacking Salary
The salary of ethical hackers in 2023 depends on various factors. These factors include experience, education, certification, skills, industry, company, location, etc. According to Glassdoor, the average salary of an ethical hacker in the US ranges between $89,043 to $106,198 per year. The salary can also increase with additional certifications.
The salary of ethical hackers in other countries may differ depending on the cost of living, demand and supply, currency exchange rate, and other factors. Here are some examples of the average annual salaries of ethical hackers in different countries as of January 2023, according to Payscale:
- India: ₹5,97,000
- United Kingdom: £46,500
- Canada: C$78,000
- Australia: A$92,000
- Germany: €55,000
- Singapore: S$72,00
Top Job Profiles of Ethical Hackers in 2023
Ethical hackers are professionals who use their hacking skills to test and improve the security of computer systems and networks. They are in high demand in various industries, especially those that deal with sensitive data and information. Some of the top job profiles for ethical hackers in 2023 are:
Application Security Developer
Average salary: $97,537/yr
An application security developer is responsible for designing, developing, testing, and maintaining secure applications & software. They use various tools and techniques to identify and fix security vulnerabilities in the code. Moreover, they ensure compliance with security standards and best practices.
Penetration Tester
Average salary: $1,03,031/yr
A penetration tester simulates real-world cyberattacks on a system or network to assess its security level and find weaknesses. They use various methods such as phishing, malware injection, brute force attacks, and social engineering to test the system’s defenses.
Threat Analyst
Average salary: $54,291/yr
A threat analyst monitors and analyzes the cyber threats and risks facing an organization or a system. They use various sources of intelligence such as logs, alerts, reports, and feeds to identify and prioritize potential threats.
Security Engineer
Average salary: $1,18,260/yr
A security engineer is a security professional who designs, implements, maintains, and troubleshoots the security infrastructure and systems of an organization or a system. They use various tools and technologies such as firewalls, antivirus software, encryption, authentication, and access control to protect the system from unauthorized access and attacks.
Infrastructure Security Engineer
Average salary: $89,731/yr
An infrastructure security engineer is a security professional who focuses on the security of the physical and virtual infrastructure of an organization or a system. They use various tools and techniques to secure the network, servers, cloud, devices, and data centers from cyber threats and ensure their availability, reliability, and performance. The average salary of an infrastructure security engineer in US dollars is around $107,000 per year1.
These are just some examples of the job profiles of ethical hackers in 2023. There may be other job profiles that require ethical hacking skills and knowledge.
Source: Glassdoor
Industries that are hiring Ethical Hackers in 2023
Ethical hackers are in high demand in various industries and sectors that need to protect their systems and data from cyberattacks. Some of the industries and sectors hiring ethical hackers in 2023 are:
IT and Software
- IT and software companies are the main recruiters of ethical hackers, as they need to secure their products and services from malicious hackers.
- They hire ethical hackers to test their applications, software, networks, and systems for security flaws and vulnerabilities.
- Some of the top IT and software companies hiring ethical hackers are Accenture, HCL, Wipro, Infosys, Genpact, IBM, TCS, Tech Mahindra, and Airtel23.
Banking and Finance
- Banking and finance companies deal with sensitive and confidential information such as customer data, transactions, accounts, and money.
- They need to protect their systems and data from cyber threats such as identity theft, fraud, phishing, and ransomware. They hire ethical hackers to conduct penetration testing, vulnerability assessment, and security auditing for their systems and networks.
- Some of the top banking and finance companies hiring ethical hackers are Bank of America, Citibank, HDFC Bank, ICICI Bank, Axis Bank, and SBI2.
Government and Defense
- Government and defence agencies are responsible for national security and public safety.
- They need to protect their systems and data from cyberattacks by hostile actors such as terrorists, hackers, spies, and criminals.
- They hire ethical hackers to perform security analysis, threat intelligence, cyber warfare, and digital forensics for their systems and networks.
- Some of the top government and defense agencies hiring ethical hackers are NSA, CIA, FBI, NIA, CBI, DRDO, ISRO, and Indian Army2.
E-commerce and Retail
- E-commerce and retail companies operate online platforms that offer various products and services to customers.
- They need to protect their systems and data from cyberattacks that can compromise customer privacy, trust, and loyalty.
- They hire ethical hackers to ensure the security and integrity of their websites, apps, databases, and payment systems.
- Some of the top e-commerce and retail companies hiring ethical hackers are Amazon, Flipkart, Myntra, Snapdeal, Walmart, and Reliance2.
Healthcare and Pharma
- Healthcare and pharma companies deal with sensitive and critical information such as patient records, medical reports, prescriptions, and research data.
- They need to protect their systems and data from cyberattacks that can endanger patient health, safety, and privacy.
- They hire ethical hackers to safeguard their systems and networks from malware, data breaches, and cyber espionage.
Top Certifications and Courses in Ethical Hacking
If you want to pursue a career in ethical hacking, penetration testing, or other offensive cybersecurity fields, you might want to consider getting one of these four reputable certifications. They can help you demonstrate your skills and knowledge to potential employers and boost your earning potential.
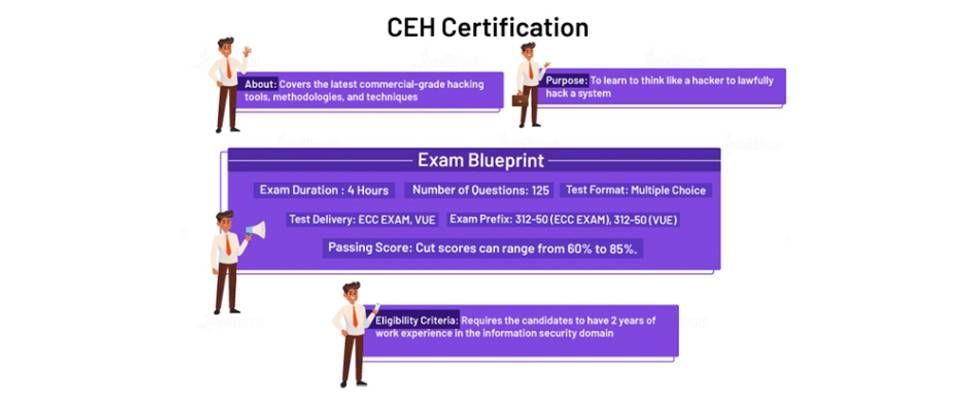
This certification from the EC-Council is one of the most recognized and sought-after in the cybersecurity industry. It shows that you have the skills and knowledge to perform ethical hacking tasks such as penetration testing, attack vectors, detection, and prevention.
- Requirements: You need to have at least two years of information security experience to take the CEH exam. Alternatively, you can complete an official EC-Council training course to waive this requirement.
- Cost: The exam fee ranges from $950 to $1,199 depending on where you take it.
- Salary: $92,000
- Tip for passing the exam: The EC-Council provides a free CEH Exam Blueprint that outlines the topics that are covered in the 125 multiple-choice questions. You can also use the practice exams from Boson to get familiar with the types of questions and topics that will appear on the actual exam.
This certification is designed for those who want to specialize in penetration testing. It proves that you can conduct comprehensive penetration tests using the latest techniques and methodologies. It covers topics such as test planning, scoping, and recon; scanning and exploitation; password attacks; and web application pen testing.
- Requirements: There are no specific prerequisites for taking the GPEN exam.
- Cost: $1,699
- Salary: $104,000
- Tip for passing the exam: You can use the two practice tests that are included when you register for the exam. These tests will help you simulate the real exam environment and identify your strengths and weaknesses.
This exam from CompTIA is unique in that it has both multiple-choice and performance-based questions (questions that test your ability to solve problems in a simulated environment). The exam tests your ability to perform penetration tests in different scenarios, such as cloud, hybrid, web application, onsite, and Internet of things (IoT) environments.
- Requirements: There are no mandatory prerequisites, but CompTIA recommends that you have three to four years of information security experience and that you have mastered the materials covered in the Network+ and Security+ exams.
- Cost: $370
- Salary: $88,206 (for penetration tester)
- Tip for passing the exam: The PenTest+ exam tests your knowledge in different ways, so it’s a good idea to use different study resources to prepare. Here are some resources that previous test takers have found helpful:
This certification is highly respected and sought-after by pen testers, ethical hackers, and other offensive security professionals. It tests your ability to breach a series of target machines and produce detailed reports for each attack.
- Requirements: There are no formal requirements to sit the exam, though Offensive Security recommends that you be familiar with networking, bash scripting, Perl or Python, and Linux. You may also consider taking the Penetration Testing with Kali course prior to taking the exam.
- Cost: From $999
- Salary: $96,000
- Tip for passing the exam: Practice taking technical notes as you work through boxes or challenges during your preparation. Organize your notes with a table of contents so you can quickly access what you need on test day if you encounter a challenge that looks familiar. It’s also a good idea to prepare a report template for exploits ahead of the exam.
Top Companies hiring Ethical Hackers in 2023
There are many companies that hire ethical hackers for various purposes, such as testing their security systems, finding, and fixing vulnerabilities, and preventing cyberattacks. Some of the best companies for ethical hackers are those that offer a high salary, a challenging and rewarding work environment, a supportive and collaborative culture, and opportunities for learning and growth. Some of the top companies hiring ethical hackers in 2023 are:
- Tesla: Tesla is a leading company in the electric vehicle and clean energy industry. Tesla hires ethical hackers to test its products and systems for security flaws and improve its cyber defences. Tesla offers a high salary, stock options, and bonuses to its ethical hackers, as well as a chance to work on innovative and cutting-edge projects.
- HackerOne: HackerOne is a platform that connects ethical hackers with organizations that need their services. HackerOne hosts bug bounty programs, where ethical hackers can earn rewards for finding and reporting security vulnerabilities in various systems and applications. HackerOne offers a flexible and remote work environment, a diverse and inclusive community, and a chance to work with some of the biggest names in the industry.
- Google: Google is one of the most popular and influential technology companies in the world. Google hires ethical hackers to protect its products and services from cyber threats and enhance its security posture. Google offers a competitive salary, generous benefits, and perks to its ethical hackers, as well as a culture of innovation, collaboration, and fun.
- IBM: IBM is a global leader in information technology and business solutions. IBM hires ethical hackers to conduct penetration testing, vulnerability assessment, and security consulting for its clients and partners. IBM offers a competitive salary, comprehensive benefits, and opportunities for career advancement to its ethical hackers. Moreover, they also offer access to state-of-the-art tools and technologies.
- Balbix: Balbix is a cybersecurity company that provides AI-powered solutions for risk management and threat prevention. Balbix hires ethical hackers to develop and test its products and systems for security issues and improve its security capabilities. Balbix offers a competitive salary, equity, and benefits to its ethical hackers. Moreover, they also offer a fast-paced and dynamic work environment.
Growth projection for Ethical Hacking jobs beyond 2023
The job prospects for ethical hackers are very bright beyond 2023. The demand for cybersecurity professionals is expected to rise significantly in the coming years. According to the U.S. Bureau of Labor Statistics (BLS), the employment of information security analysts, which includes ethical hackers, is projected to grow 31% from 2019 to 2029, much faster than the average for all occupations.
Some of the reasons for the growth of ethical hacking jobs
- Increasing frequency and sophistication of cyberattacks: Various sectors, such as banking, healthcare, government, retail, etc., are facing more and more cyberattacks. Cyber attackers aim to steal, damage, or disrupt their data and operations. These attacks can cause huge losses, reputational damage, legal liabilities, and customer dissatisfaction for the affected organizations. Ethical hackers can help prevent and mitigate these attacks. They can identify and exploit the vulnerabilities in the systems and networks before the malicious hackers do.
- Growing awareness and compliance of data protection laws and regulations: Organizations are becoming more aware of the importance of protecting their data. They are also complying with the relevant laws and regulations. These laws and regulations impose strict requirements and penalties for data breaches and violations. Ethical hackers can help organizations comply with these laws and regulations. They can help them by conducting regular audits, assessments, and tests of their systems and networks. This will ensure their security and privacy.
- Shortage of skilled and qualified ethical hackers in the market: There is a gap between the supply and demand of ethical hackers in the market. The demand is much higher than the supply. According to CyberSeek, a project supported by the National Initiative for Cybersecurity Education (NICE), there were 166,475 job openings for information security analysts in the U.S. as of December 2021. However, there were only 131,730 workers employed in this occupation. This means that there is a talent shortage of 34,745 workers or 26% in this field. Ethical hackers can take advantage of this gap. They can acquire relevant skills, knowledge, experience, and certifications to qualify for these jobs.
- Advancement and innovation of new technologies and tools: The cybersecurity domain is constantly evolving and innovating with new technologies and tools that require constant testing and evaluation for security vulnerabilities. For example, cloud computing, artificial intelligence, machine learning, blockchain, the Internet of things, etc., are some of the emerging technologies that pose new challenges and opportunities for ethical hackers. Ethical hackers need to stay updated and adapt to these technologies and tools to ensure their security and effectiveness.
Quick tips for college pass outs to become ethical hackers
- Learn the different types of cyber-attacks and how they work. For example, malware, phishing, denial of service, SQL injection, cross-site scripting, password cracking, wireless hacking, etc.
- Develop your skillset in programming, networking, operating systems, cryptography, and web development. You can start with languages like Python, C#, Java, or Ruby. You should also be familiar with tools like Nmap, Metasploit, Wireshark, Burp Suite, etc.
- Seek certification in IT security from reputable organizations like CompTIA, EC-Council, Offensive Security, or SANS Institute.
- Gain hands-on experience by participating in online platforms like Hack The Box, TryHackMe, VulnHub, or CTF (Capture The Flag) competitions. These platforms allow you to practice your skills in realistic scenarios and challenges.
- Build your portfolio and network by creating a blog or website to showcase your projects and achievements. You can also join online communities like Reddit, Discord, or Twitter. These platforms will offer an opportunity to learn from other ethical hackers and share your insights.
- Apply for entry-level jobs or internships in cybersecurity or ethical hacking. You can look for opportunities in various sectors like finance, healthcare, government, education, or e-commerce. You can also work as a freelancer or consultant for smaller businesses or organizations.
Take control of your career and land your dream job
sign up with us now and start applying for the best opportunities!

Conclusion
Ethical hacking is a promising and rewarding career option. Ethical hackers have the opportunity to work in various sectors and industries. If you want to pursue a career in ethical hacking, you will need to acquire the relevant skills, knowledge, and certifications. Moreover, you also need to keep yourself updated with the latest security developments and trends. You can also sign up with Olibr to find exciting software job opportunities.
Frequently Asked Questions
To begin a career in ethical hacking, you need a strong foundation in computer networks, programming languages, and operating systems.
Begin by learning the basics of networking protocols, such as TCP/IP, and familiarize yourself with programming languages like Python and C++.
Gain knowledge of popular operating systems, such as Linux and Windows. Understand web technologies, databases, and security concepts.
Explore ethical hacking tools like Nmap, Wireshark, and Metasploit.
Familiarize yourself with common vulnerabilities and their exploitation techniques.
Stay updated on the latest security news and engage in online communities to learn from experienced professionals.
Finally, consider obtaining certifications like Certified Ethical Hacker (CEH) or Offensive Security Certified Professional (OSCP) to showcase your skills.
The significance and growth of ethical hacking in the USA are substantial. With the increasing reliance on technology and growing concerns about cybersecurity, organizations across various industries are realizing the importance of proactive security measures. Professionals in the field, commonly known as ethical hackers, penetration testers, or white-hat hackers, utilize their expertise to identify vulnerabilities in computer systems and networks. Collaborating with organizations, they assess security infrastructure, conduct controlled attacks to expose weaknesses and offer a remedy. The demand for ethical hackers is consistently high, with job opportunities spanning sectors such as finance, healthcare, government, and technology. As the threat landscape continues to evolve, the necessity for skilled ethical hackers to safeguard sensitive data and systems is expected to further expand.
Python is highly recommended for ethical hacking due to its extensive library of tools and frameworks. It is versatile and can be used for various tasks such as network scanning, penetration testing, and exploit development. Python’s simplicity and readability also make it easier to quickly develop effective hacking scripts.
Job opportunities in ethical hacking include roles such as penetration tester, cybersecurity analyst, vulnerability analyst, security consultant, and security engineer. Ethical hackers play a crucial role in assisting organizations in identifying and addressing security vulnerabilities, protecting systems and data from cyber threats, and ensuring adherence to ethical and legal standards.
Ethical hacking, when practiced within legal and ethical boundaries, is viewed as a positive endeavor. It aids organizations in identifying weaknesses in their systems, leading to improved cybersecurity measures. However, engaging in hacking without proper authorization or for malicious purposes is unquestionably wrong and illegal.

